The U.S. Army’s Moses project is one of the most high-profile users of OpenSim, with a focus on training and simulations rather than on using OpenSim as a platform for a social grid.

Last Friday, project leader Douglas Maxwell sent a note to OpenSim developers disclosing four “high priority security flaws” in the OpenSim software.
“We did this out of an abundance of caution and respectfully invite their participation as we design and implement corrections,” Maxwell told Hypergrid Business.
The note was intended to serve as a notification of disclosure, prior to the public release of the vulnerabilities, but it went to an open mailing list, so the vulnerabilities are now public.
“Luckily all this set of flaws is already known by this list subscribers, so no harm done,” wrote OpenSim developer Leal Duarte, who is also known as Ubit Umarov in-world.
Here is a brief summary of the vulnerabilities.
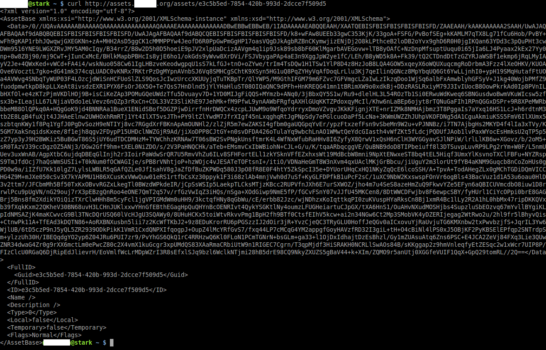
- When an OpenSim viewer communicates with the grid’s server, information about content on the grid is transmitted unencrypted, allowing eavesdroppers to get the UUIDs, which are unique object identifiers, as well as session IDs, which can make it easier to steal content and to impersonate other users.
- Scripts have the ability to make a grid participate in a distributed denial of service attack or botnets. “Grid owners would not even know their servers were being used in this way,” Maxwell wrote.
- If the grid is mis-configured in a particular way, attackers can send operating-level commands to the grid, commands which normally can only be issued by an administrator. This can be used to damage a grid.
- OpenSim does not have adequate restrictions on the languages used by scripts, potentially allowing attackers to access files on a server. “In other words, a user without credentials on your server can own it,” he said.
These vulnerabilities are a particular concern now, since Moses is about to release a Web-based viewer for OpenSim, Maxwell said.
“By January, we will be in a position to discuss openly the technical details surrounding the web viewer and the security implications,” he added.
Maxwell is the science and technology manager for virtual world strategic applications at the U.S. Army’s Simulation & Training Technology Center, which runs the Moses project.
He also released a paper about OpenSim security issues with his colleague Michael Heilman, a researcher with the University of Central Florida’s Institute for Simulation and Training and lead software engineer and architect at the University’s Virtual World Research Group.

However, not all OpenSim users and developers have the same security concerns as the U.S. Army, prioritizing flexibility, usability and connectivity instead.

That makes OpenSim more accessible, said Crista Lopes, an OpenSim core developer and a professor of informatics at the Donald Bren School of Information and Computer Sciences University of California Irvine. She recently won a $10,000 prize for her work.
“I encourage young people and newcomers to dabble into security issues of complex software,” Lopes told Hypergrid Business. “OpenSim is a great platform to learn about them.”
She is also the inventor of the hypergrid, which allows user to teleport between grids, and even to move content and send instant messages from one grid to another.
Moses does not allow hypergrid teleports to other grids.
Meanwhile, grid owners already have many options for increasing the security of their grids.

“There are many options out there,” said Josh Boam, founder of the SkyLife Grid and hosting company. That includes replacing the default back-end grid management tool, which is called Robust, as SkyLife grid did. Their version is called PHP Robust.
“Everything is done via a Web server and is much faster and can handle more load,” he told Hypergrid Business. “Security in OpenSim can only be so good as the people hosting the regions. Firewalls and IP rules with access restrictions is the way to go.”
In addition, there is a limit to how much can be done to stop hackers.
“It really doesn’t matter how secure you try and make things, someone will always try and get in,” said Cliff Hopkins, founder of the Genesis Metaverse grid and hosting company.

But this is a good time to discuss security issues, he said, since Linden Lab is working on migrating uses from Second Life to its new Sansar platform.
“OpenSim is growing and Second Life is dying,” he said.
In fact, Second Life’s average concurrency has fallen by more than 34 percent since its peak in 2010, according to data from Grid Survey.
OpenSim offers a low-cost alternative for Second Life users, he said. And users won’t have to learn a new interface if they switch from Second Life to OpenSim.
In fact, some of the security issues have to do with decisions made by Linden Lab, the maker of Second Life. Since OpenSim currently uses the same viewers as Second Life, and so has to support the existing communication standards.

“They are rooted in the Linden Labs protocol design,” OpenSim spokeswoman Melanie Thielker told Hypergrid Business. “The Linden Lab viewer allows insecure HTTP connections and also uses unencrypted UDP network transmissions. While the HTTP part can be secured by using an expensive wildcard certificate, the UDP part cannot. This is not a flaw in OpenSimulator, but rather in the design that came from Linden Lab and stems from a less security-conscious era.”
Meanwhile, the issues connected to executing commands and uses scripting languages other than LSL are also nothing new, she added.
“Please note how he states that a ‘misconfigured’ server is open to attack,” she said. “That is simply because these dangerous options are disabled by default.”
OpenSim developers prioritize freedom of choice, she said.
“I am pretty sure the product Moses will eventually arrive at will not have these potential vulnerabilities, but that will be because it will be lacking these choices,” she said.
Finally, the ability to abuse scripts as relays and cutouts is also known, she said, and also exists in Second Life.
“Second Life has entire sims that contain 15,000Â simple boxes with 255 scripts each, each of those scripts executes
malicious probes against Internet hosts or sends massive amounts of spam to open relays,” she said. “Linden Lab is aware of it and shuts them down if the activity is criminal, but not if it’s just spamming or non-exploiting probes. Therefore, OpenSimulator is again not in a position to prohibit this without sacrificing compatibility and breaking existing content.”
Another vulnerability mentioned, where content is scraped from a grid, is only possible on grids that allow users to connect self-hosted regions, said Thielker, which is a small percentage of all the public grids.
“It isn’t possible on grids that don’t allow people to connect their own regions as OSGrid does,” she said.
Thielker is also the founder of the commercial Avination grid, which donated a large amount of code to the OpenSim project last fall, which has been integrated into the soon-to-be-released 0.9.0 release of OpenSim.
Its top competitor, InWorldz, which is the most popular grid running the OpenSim software, also open sourced its code last fall. That code, Halcyon, is a version of OpenSim designed for greater security — and has been adopted by Moses as the basis for its grid.
While both InWorldz and Avination are closed grids, with users not able to teleport to other worlds, the main branch of OpenSim fully supports the hypergrid, and Halcyon does not, though Moses may add hypergrid support.
The new browser-based viewer that Moses will release later on this fall will be designed to work with the Halcyon branch of OpenSim, and it is not yet clear how much additional work it will take to make it work with standard OpenSim.
A browser-based viewer will make OpenSim much easier to use. Currently, users have to download and install special viewer software. And if a grid is not on the default grid list that comes with the viewer, users have to manually add it.
Raising the issue of the OpenSim security flaws might cause some grid owners to consider switching to Halcyon, she suggested, providing some additional momentum for the Halcyon project and steering the OpenSim community more towards the Army’s vision of the future of OpenSim.
“It’s a sad thing that the U.S. Army has to resort to such methods,” she said.
- Kitely Mega Worlds on sale for $90 per month - July 19, 2024
- OpenSim regions up, actives down with summer heat - July 15, 2024
- People think AIs are conscious. What could this mean for bots in OpenSim? - July 12, 2024
